Initially, our technical experts have highlighted the list of research topics in computer networks for your ease.
- A dynamic e-epidemic model for the attack against the spread of virus in computer network
- Sensing and compensating the thermal deformation of a computer numerical control grinding machine using a hybrid deep learning neural network
- Improve computer visualization of architecture based on the bayesian network
- User acceptance in a computer supported collaborative learning (CSCL) environment with social network awareness (SNA) support
In addition, we highlighted some sample source code based on Cooja and C mainly for the sink configuration.
static struct simple_udp_connection unicast_connection;
PROCESS(mobile_node_process, "Sink node");
AUTOSTART_PROCESSES(&mobile_node_process);
static void
mobile(struct simple_udp_connection *c,
const uip_ipaddr_t *sender_addr,
uint16_t sender_port,
const uip_ipaddr_t *mobile_addr,
uint16_t mobile_port,
const uint8_t *data,
uint16_t datalen)
{
printf("Data received from ");
uip_debug_ipaddr_print(sender_addr);
printf(" on port %d from port %d with length %d: '%s'\n",
mobile_port, sender_port, datalen, data);
}
static uip_ipaddr_t *
set_global_address(void)
{
static uip_ipaddr_t ipaddr;
int i;
uint8_t state;
uip_ip6addr(&ipaddr, UIP_DS6_DEFAULT_PREFIX, 0, 0, 0, 0, 0, 0, 0);
uip_ds6_set_addr_iid(&ipaddr, &uip_lladdr);
uip_ds6_addr_add(&ipaddr, 0, ADDR_AUTOCONF);
printf("IPv6 addresses: ");
for(i = 0; i < UIP_DS6_ADDR_NB; i++) {
state = uip_ds6_if.addr_list[i].state;
if(uip_ds6_if.addr_list[i].isused &&
(state == ADDR_TENTATIVE || state == ADDR_PREFERRED)) {
uip_debug_ipaddr_print(&uip_ds6_if.addr_list[i].ipaddr);
printf("\n");
}
}
return &ipaddr;
}
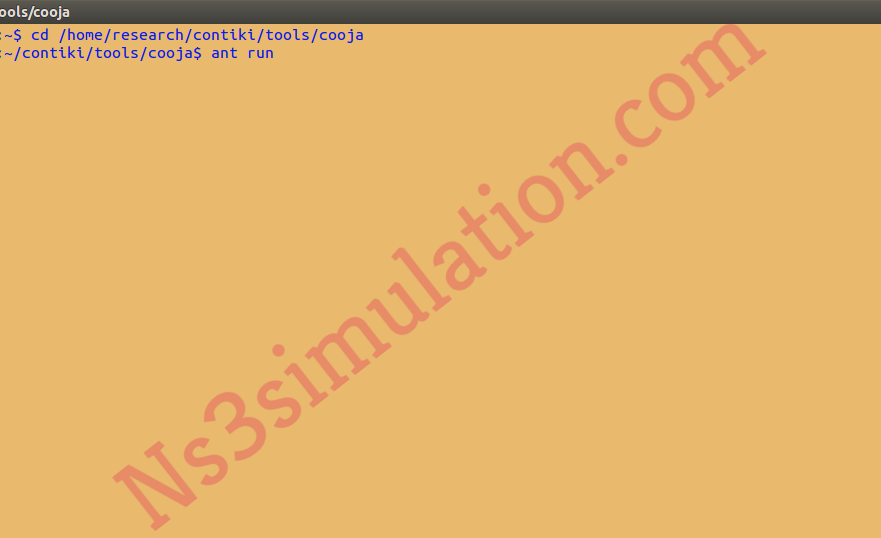
On the other hand, we have executed the source code based on computer network projects through the implementation of the below mentioned commands in the terminal.
cd /home/research/contiki/tools/cooja
ant run
Following that, the Cooja simulator has been started and we have to select the configuration file in the Contiki.

The research scholars can contact us to clarify the doubts based implementing the computer network projects.











































