Sure, our resource team will provide the complete research support for the research scholars to enhance their network skills and build the network intrusion detection system using python. Let’s start this article with the list of algorithms that are deployed to implement the network intrusion detection system.
Algorithms to Detect Intrusions
- Fully connected feed forward neural network
- CNN with metaheuristics algorithm
- Improved GAN
- Attention based neural network
- Hybrid CNN and LSTM
Along with that, our technical professionals have highlighted some list of topics in network intrusion detection systems which are implemented by our development team.
Emerging Research Topics in IDS
- False data injection attack detection model for cyber-attack resilient energy forecasting
- Adaptive network security system for IoT enabled maritime transportation
- Transfer learning approach to IDS on cloud IoT devices using optimized CNN
- Novel detection approach of unknown cyber-attacks for intra vehicle networks using recurrence plots and neural networks
- In vehicle CAN bus tampering attacks detection for connected and autonomous vehicles using an improved isolation forest method
- Optimization of intrusion detection using likely point PSO and enhanced LSTM-RNN hybrid technique in communication networks
- Cyber-attack correlation and mitigation for distribution systems via machine learning
- Novel online network intrusion detection system for industrial IoT based on OI-SVDD and AS-ELM
- Deep active learning intrusion detection and load balancing in software-defined vehicular networks
- Dew cloud based hierarchical federated learning for intrusion detection in IoMT
- TOW-IDS: Intrusion detection system based on three overlapped wavelets for automotive Ethernet
- Online approach to covert attack detection and identification in power systems
When we are addressing the resource to build intrusion detection system, we have provided the source code in python.
Python Based Resource for Network IDS
def model_perfomance(y_pred, y_prob, y_true):
tn, fp, fn, tp = confusion_matrix(y_true, y_pred).ravel()
recall = tp / (tp+fn)
specificity = tn / (tn+fp)
gmean = np.sqrt(recall * specificity)
auc = roc_auc_score(y_true, y_prob)
f_score = f1_score(y_true, y_pred)
coverage = weighted_coverage(y_true, y_prob)
acc = accuracy_score(y_true, y_pred)
performance = [auc, coverage, f_score, gmean, recall, acc]
return np.array(performance)
rf = RandomForestClassifier(n_estimators=350, max_depth=6, random_state=2018)
xgb = XGBClassifier(n_estimators=350, learning_rate=0.25, max_depth=6, n_jobs=-1, random_state=2018)
svm = SVC(C=1.0, kernel='rbf', gamma='auto', probability=True, degree=3, random_state=2018)
lr = LogisticRegression(penalty='l2', C=1.0, solver='lbfgs', max_iter=1200, random_state=2019, n_jobs=-1)
def performance_contrast(seed, cost_fn=1.5, cost_fp=1.0, clf_one=xgb, clf_two=rf):
start = time.time()
P, U, U_label = generate_pudata(seed)
print('Seed:{:}, P Shape:{:}, U Shape:
{:}'.format(seed, P.shape, U.shape))
adoa = ADOA(P, U, clf_one)
y_pred, y_prob = adoa.predict()
adoa_performance = model_perfomance(y_pred, y_prob, U_label)
X_train = np.r_[P, U]
y_train = np.r_[np.ones(len(P)),
np.zeros(len(U))]
svm.fit(X_train, y_train, sample_weight=[cost_fn if i else cost_fp for i in y_train])
y_pred, y_prob = svm.predict(U),
svm.predict_proba(U)[:, -1]
svm_performance = model_perfomance(y_pred, y_prob, U_label)
pos_weight = len(U) / len(X_train)
neg_weight = 1 - pos_weight
lr.fit(X_train, y_train, sample_weight=[pos_weight if i else neg_weight for i in y_train])
y_pred, y_prob = lr.predict(U),
lr.predict_proba(U)[:, -1]
lr_performance = model_perfomance(y_pred, y_prob, U_label)
pul_csl= pul(P, U, cost_fn=cost_fn, cost_fp=cost_fp, clf_one=clf_one, clf_two=clf_two, over_sample=False)
y_pred, y_prob = pul_csl.predict()
pul_csl_performance = model_perfomance(y_pred, y_prob, U_label)
metrics = ['AUC', 'Coverage', 'F1_Score', 'G_Mean', 'Recall', 'ACC']
models = ['ADOA', 'Biased_SVM', 'Weighted_LR', 'PUL_CostSensitive']
list_ = [adoa_performance, svm_performance, lr_performance, pul_csl_performance]
performance = pd.DataFrame(list_, columns=metrics, index=models)
algorithms = [performance[i].idxmax() for i in metrics]
performance.loc['The Best Algorithm', :] = algorithms
print(algorithms)
decription = 'The evaluation of the algorithm has been completed.'
print(decription, 'Running_Time:
{:.2f}s\n'.format(time.time()-start))
return performance
seeds = np.random.RandomState(2019).choice(range(1000), size=10, replace=False)
contrast = [performance_contrast(seed) for seed in seeds]
contrast_concat = np.concatenate([contrast[i] for i in range(len(contrast))])
data_names = np.array([['Dataset_' + str(i)]*5 for i in range(len(seeds))]).ravel()
models = ['ADOA', 'Biased_SVM',
'Weighted_LR', 'PUL_CostSensitive',
'The Best Algorithm'] * len(seeds) #
CostSensitive
metrics = ['AUC', 'Coverage', 'F1_Score', 'G_Mean', 'Recall', 'ACC']
arrays = [data_names, models]
idx = pd.MultiIndex.from_arrays(arrays, names=('VerifyData', 'Algorithm'))
contrast_result = pd.DataFrame(contrast_concat, index=idx, columns=metrics)
print(contrast_result)
best_algo = contrast_result.query("Algorithm == 'The Best Algorithm'")
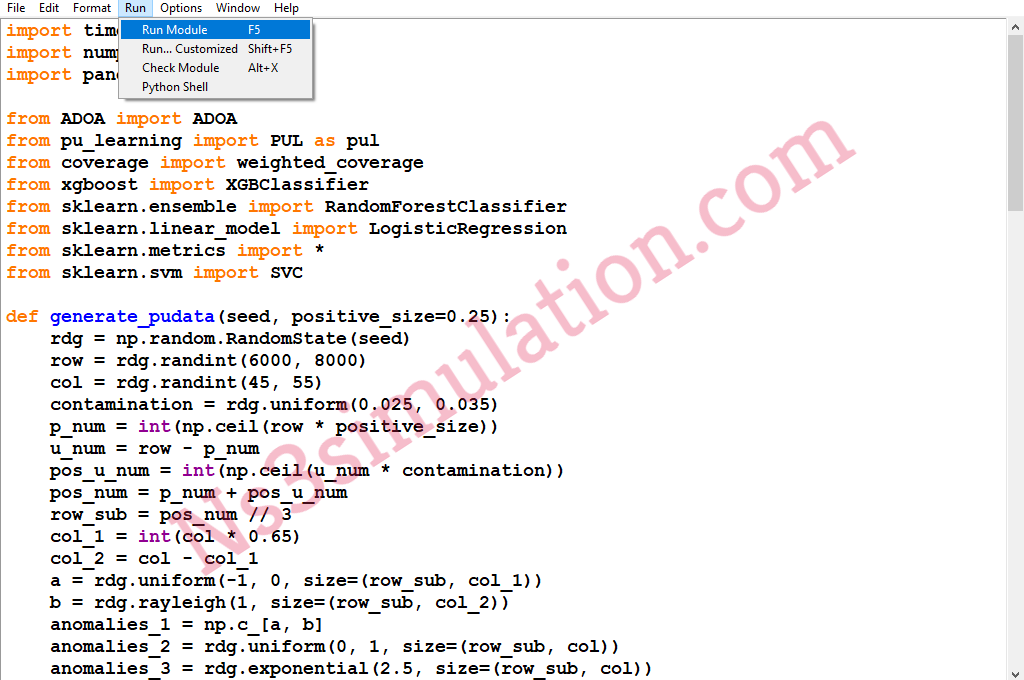
Execution of Python Based IDS
We have to open the Python IDE and the file has to be opened as mentioned in the following image.

Following that, we have to browse the python source code file to proceed with the execution process.

Finally, we have to execute the python IDE source code just by clicking the option namely, run module.
If you guys have to know more about the implementation of intrusion detection system, then reach us and acquire more.











































