In general, our research professionals have presented this article “ns3 intrusion detection” with all the required keynotes about significance of intrusion detection system and network simulator 3. Initially, we have listed the types of intrusion detection,
- Network intrusion detection system
- It is the most common type of IDS to recognize the anomalies over the network traffic and it is functioning as the promiscuous network
- Host intrusion detection system
- It is proposed to recognize the intrusion through the environment observation and it is deployed to detect the malicious actions
Hereby, our research experts have enlisted the attacks that are detected through the network simulator 3.
- SQL injection
- Cross site scripting
- Malware attacks
- Phishing attack
- Blackhole attack
- Side channel attacks
- Eavesdropping
- Spoofing attacks
- Flooding attacks
- Probing attacks
- Distributed denial of service
- Denial of service
- Sniffing attacks
For your additional reference, the algorithms those are functional in the process of intrusion detection are highlighted in the following.
- Capsule network (CapsNet)
- Deep neural network (DNN)
- Support vector machine (SVM)
- Recurrent neural networks (RNN)
- Long short term memory (LSTM)
- Back propagation neural network (BPNN)
- Graph neural network (GNN)
- Light gradient boosting machine (LGBM)
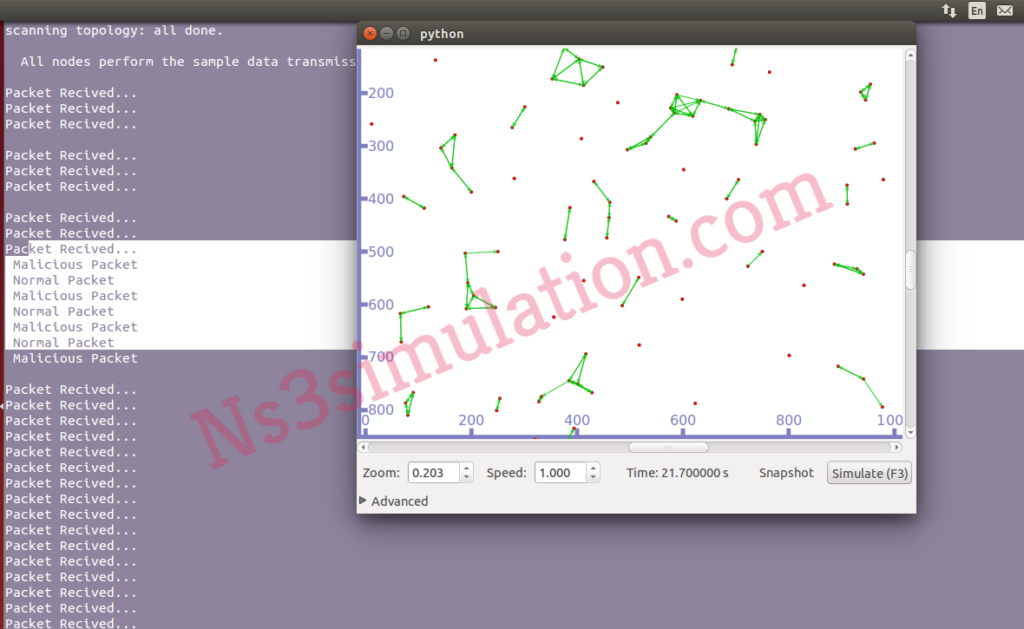
As well as, it’s most important to implement the ns3 simulation file and it is deployed to detect the intrusion through the execution of the following commands.
cd /home/research/ns-allinone-3.26/ns-3.26
sudo ./waf --run Main --vis

In an additional note, you guys can contact us at any time to clarify your doubts.











































