As the matter of fact, PhD research scholars are struggling to select a research topic for their research. Thus, our technical folks have described this article with the list of emerging research topics in information security to make that task even easier. Come! Let’s take a glaze over the list of research topics in information security.
- Interoperable secure communications
- Data priority computation
- Upcoming attacks detection by IDS
- Security attacks and challenges
- Dynamic authentication
Information Security Projects
For your reference, our research experts have highlighted latest research topics in the field of information security so make use of it.
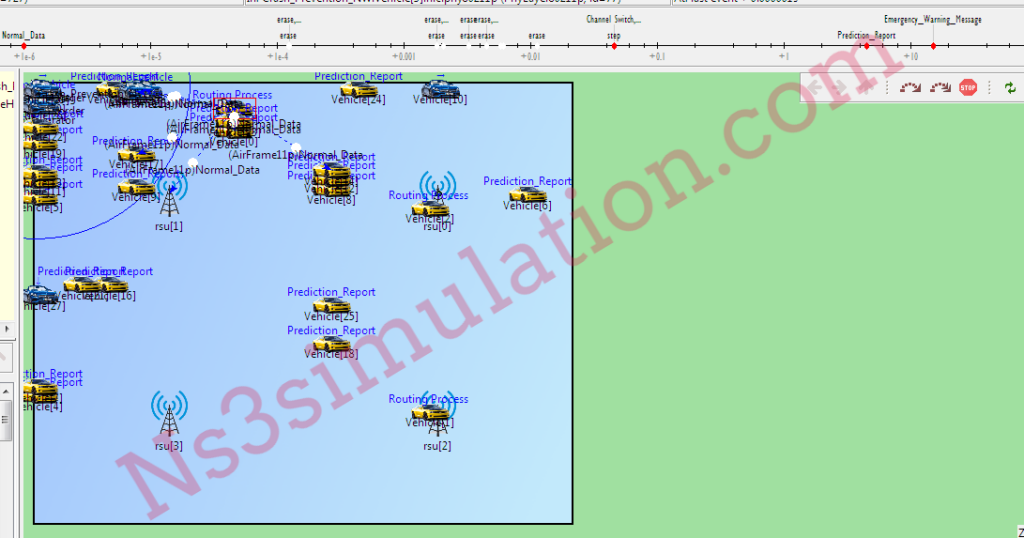
- Blockchain & mutual clustering in C-V2X networks using real time information security transmission
- Utilization of machine learning based data for automated security risk identification
- Enhancement of privacy and security for private information retrieval using wiretap channel II
- Dynamic prediction against information security ruin using neural variability fingerprint of an individual
- Field zones security in industrial control systems using software defined security techniques
- Branch hidden ABO-LTFs for leakage prevention CCA security
- Deployment of virtual boundary recognition to control the sensitive information flow of tenants
- Multiple access mobile edge computing: Physical layer approaches for information security enhancement in heterogeneous IoT
- Enhancing vehicular network communications using secure many to many authentication and key agreement technique
- Pacts of sharing security information via private and public assessments
- Improving DMM based smart home IoT networks through route optimization of security protocols
- Modular encryption standard for security enhancement of health information in mobile cloud computing
- Advancement in information security storage using reversible stimuli lanthanide polyoxometalate luminescent hydrogel
- Key agreements and encryption in information theoretic cryptography using security formulations
- Utilization of multi sensor data fusion for the security enhancement in flowmeter communication network
- Demonstration of quantitative hardware security properties using multi flow information tracking approach
- Active security processor for built in security computer with security architecture
- IS-CHEC information security human reliability analysis (HRA) technique for the viewpoint of employee about information security related human error in healthcare
- Deployment of hierarchical regression to recognize the effect of data breach publicity on information security awareness
- Dynamic process of optimal selection of initiative information security defensive actions using decision support system
Our technical folks are always ready to provide the appropriate guidance for the research scholars. So, reach us and aid more











































