The term research proposal is referring to the writing work in which undertaking research’s detailed explanations is given in a few words. A research proposal is always known as the comprehensive statement of proposing research. “This is the article which is going to tell you the most awaited secret about how to get PhD research proposal help”
Generally, a proposal’s quality is determined by its practicability as it is going to play a vital role in the technology. According to our technical experts, doing researches are like biting sugarcane. Besides, it may daunt to beginners and naïve individuals as they are not having experiences.
But nothing to worry about, by learning concepts you can become master in any kind of technology. In reality, research proposals are being reviewed by a committee which is headed by a panel of judges. For this, a researcher has to prove that they are having valid research ideas and problems.
In short, proving something before the community utilizing representing a writing workshop in the initial is called a research proposal. Let us have further fascinating enlightenments on PhD research proposal help service. To the point, our technical experts brought the aspects contained in the proposal first.
What’s included in Research Proposal?
- Review of literature
- Problem statement
- Summary
Itemized above are the major things that are presented in a typical PhD research proposal. Generally, problems statements are stated to justify the significance of proposed research problems utilizing empirical and hypothetical manners.
Before mentioning the research problem, one should thoroughly investigate the related literature papers to find that research problem. Usually, research is like a lifetime experience. For example, people learn from mistakes! Likewise, other researchers’ mistakes are being hustled by other upcoming researchers to patch up those research gaps in the emerging technologies.
At last, we’ve highlighted the summary right! That summary of the study must include the following aspects,
- Testing techniques for hypothesis
- Research question addressing
- Evidence interpreting ways
- Evidence amassing stratagems
- Tested hypothetical theories & research models
- Answering capability
- Context of the framework
- Interest of illumination
- Theoretical functioning properties discussion
Above mentioned aspects may vary according to the discipline or domain selection. The said aspects are often called as main components of the PhD research paper. Finally, discussing the evidence collected is different corresponding to academic studies such as economics and commerce.
“Best proposals moves forward by effortless and graceful flow like an uninterrupted river”
These clear elucidations on research proposal inclusions would impact something in your brain. By brainstorming various concepts of proposal writing, even an inexperienced scholar also can draft a very good PhD research proposal. However, it needs sound and effective practices in related studies ranging over technical eras.
At this time, everyone should note the structure of the same proposal. As a matter of fact, it differs from university to university according to their guidelines amended. But, here we are going to bring out the most appropriate structure in light of your visions. Come let us have the elaborated explanations about PhD research proposal help service. We help to write up a research proposal based on the following structure.
What is the Structure of a PhD Research Proposal?
- Introduction
- In the primer part, the main research problems are indicated in terms of how it is relating to the proposing study
- Also, gives statements on how it is going to be analyzed through what methods
- Furthermore, give strong specifications on undertaking research’s importance
- Study Background
- In the study’s background current state of the art is described very specifically
- Giving brief substantial key information is essential here
- Literature Review
- Literature reviews are often called related works which are conducted to find gaps in the previous researches
- Also leads to offer proper hypotheses and its elaborate descriptions
- Statement of Problem
- Problem statements are indicating the current issues aroused in the proposed study
- It also tells the reason behind addressed problems and ensures its novelty
- Research Objectives
- Usually, research works are pillared with more than 5 objectives
- Research Questions
- It is the transformation of research main objectives utilizing its scope
- As wells as determined to improvise the field in which it was proposed
- Research Scope
- In this section, investigating research’s significance is plotted very clearly
- Functioning Descriptions
- These are the explanation sections of driving and essential operations
- Methodologies
- This section not only tells about the proposed methodology but also design and approaches with validations
- For example, if sampling methods proposed principle considerations will be explained respectively
- Study Limitations
- Here, the proposed research work’s incapabilities are stated in terms of out of scope, limited coverage, and boundaries
- Research Summary
- Here, findings’ implications to the investigated area are clearly conveyed
- In short, it is the collection of restatements about the entire research purpose, addressed questions and their solutions
- Bibliography
- It is otherwise known as references which are significantly told about all those materials and sources used
In general, bibliographies are simple just like the links situated in websites, social media, YouTube and emails, etc. Further, we hope that you would have known about the reasons behind tagging those links. These are done to refer to something related to the current undertaking process. On the other hand, mentioning the research area is very important.
For example, if the research is examined in the areas of technology then specify the technology in which you are performing (deep learning, machine learning, and artificial intelligence). To be frank, we are giving our PhD research proposal help and support by 24 / 7. If the students are belonging to different geographical locations, we are also offering digital tutorials.
As our institution has consisted of experienced professional writers, plagiarism-free papers are effortlessly given for every single time of delivery. Our dedication is recognized by many of the developer and research reviewing communities such as Springer, ACM, IEEE, and many more. In general, visualizing the components of a research proposal could impact a difficulty since we are accustomed to several advanced tools. Those tools are significantly enriching the readability and accessibility of proposal papers in an incredible way.
While drafting a PhD research proposal students are generally making mistakes and flaws. These mistakes are making their proposals a little bit secondary. By avoiding several mistakes in research proposal writing everything will be alright! For this, you just want to trespass this passage that’s it.
What are Common Mistakes in Writing a Research Proposal?
- Lack of APA writing styles
- Vague and very short explanations
- Improper references & gaps in significant citations
- Messed up map directions
- Crisscross explanation importance
- Lack of coherency & manipulative developments
- Elapses in research question scope
- Incorrect representation of other experiential & hypothetical contributions
- Unmanageable research boundary restrictions
- Unsuitable research question contexts
The above mentioned are the various mistakes done with or without the knowledge of scholars widely. Primarily, try to avoid giving lengthy explanations on minor problems and giving inadequate explanations on major research problems. The papers done from our side are always replicating the first-class quality.
Concurrently, we are injecting innovations and professionalism together to your proposals when you are availing of our PhD research proposal help. Every research proposal is subject to novelty and originality. As well as our deliveries are on time with affordable prices. Thus our main motto is to satisfy the willing student’s requirements since we are not that much bothered about high costs.
As many of the scholars are approaching us and asking for our writing procedures in research proposals hence we would like to give some crisp points about how we write the PhD research proposal. Come let us also learn about it.
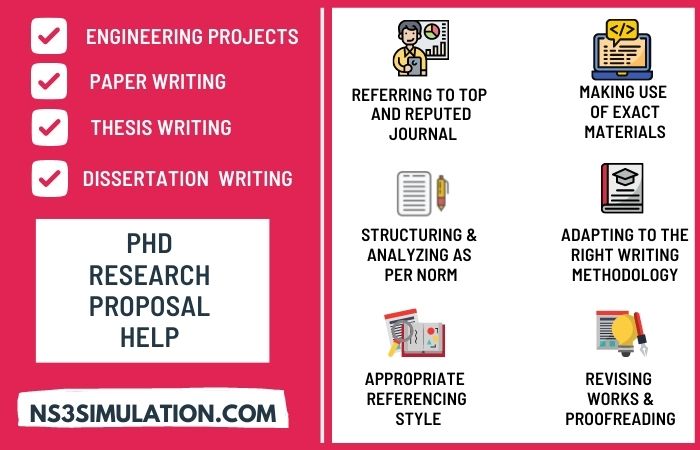
Our PhD Research Proposal Help?
- Referring to top and reputed journals
- Making use of exact materials
- Structuring & analyzing as per norms
- Adapting to the right writing methodology
- Appropriate referencing styles
- Revising works & proofreading
This is how we start and end our writing processes. Besides, we do prefer some more tactics and techniques according to the nature of the research undertaken. On account of our technical experts’ dedication, we are continuously reaching great heights in the technical industry.
Out technical writers’ consistency cannot be stated in words as they are not limited to any kind of difficulties as well as our writings are reader-oriented. PhD research proposals can be done in the various emerging technologies. For your better understanding, we brought out some interesting topics based on those technologies from our paper writing guidance team.
What are the Good Topics to write PhD Research Proposal?
- Communication Technologies
- Energy Efficiency & Green Communication Networks
- Beamforming & Multi-Antenna Structures
- Cooperative & Ad-Hoc Communications
- Machine to Machine & Desktop to Desktop Communications
- Actuator & Wireless Sensor Networks
- Cognitive Radio Networks
- Self-Driven or Automated Networks
- IoT Based Apps & Protocols
- Big Data Networking
- Network Consistency & Reliability
- Disaster Retort, Safety & Amenity based Technologies
- Small Cells & Heterogeneous Networks
- 5G Mobile Communications
- Internet of Things
- Semantic Technologies & Web of Things
- IoT using Web Technologies
- WoT & IoT Discoveries
- Security & Privacy Measures in WoT
- Industrial Web of Things
- WoT & 5G Integrations
- Cloud, Fog & Edge Computing
- Industrial Scenarios using Interoperability
- Wireless and Mobile Networks
- Switching & Routing Algorithms
- Security & Management in Networks
- Vehicle-Everything (V2X)
- Wireless Sensor Network
- Resource Management & Quality of Services
- Congestion or Traffic Control Mechanisms
- 5th Generation Apps & Sensible IoT’s
- Spectrum Allocation & Managing
- Network Function Virtualization & Software Defined Network
- Next-Gen Network Protocols
- Wireless & Mobile Communication Networks
- Sensor & Mobile Adhoc Networks
- Broadband & Internet Access Technologies
- Heterogeneous Wireless Networks
As we all know that technologies are the lifeblood of our modern world. Essentially, technologies are subject to several loopholes and pitfalls. That is cannot be avoided. However, improvising the technical edges can make a big difference. So that researchers are playing a vital role to identify the research gaps still existing in irreplaceable technologies.
In short, we are supposing you, people, to strengthen up the technologies using your significant contributions. Reach our PhD Research Proposal Help Panel for further assistance. Let’s hope for the best.
“Tremendous victories are on the track and keep your concentrations wise”